Security Checklists · May 2, 2026
7-Step Security Checklist to Protect Your AI-Powered Innovator Visa Application
Protect your AI-powered Innovator Visa submission with our 7-step security checklist, ensuring robust defence at every stage.

Nailing Your AI Innovator Visa Security from Day One
Every entrepreneur knows the UK Innovator Founder Visa process is rigorous. Throw AI into the mix and you need an even tighter defence. That’s where an application checklist AI comes in. It’s not just a list—it’s your digital guardian. It flags weak spots before Home Office officers spot them. It ensures your business plan, founder profile and tech stack meet strict criteria, day or night.
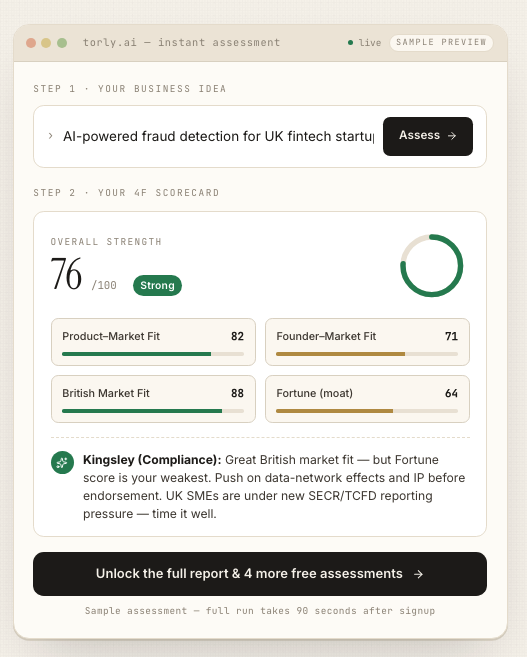
You can streamline your entire submission with Torly.ai’s intelligent analysis layer. It runs instant, multi-layered checks on your documents, technology setup and even team structure. Ready to stay ahead of the curve? Application Checklist AI: AI-Powered UK Innovator Visa Application Assistant
Below, you’ll find a 7-step security checklist that guards every corner of your application. Consider it the backbone of a bullet-proof filing. And yes, this is the same rigour we use to power our AI-driven platform and your next big milestone.
1. Fortify Your Authentication and Access Controls
Weak credentials are a hacker’s first port of call. Step one in your application checklist AI is to enforce strong, multifactor authentication for every account tied to your visa submission. That includes:
- Personal and team e-mail addresses
- Cloud dashboards hosting your business plan drafts
- Torly.ai portal access
Use time-based one-time passwords (TOTP) or hardware keys. Remove inactive accounts promptly. Limit privilege levels by role; a founder needs more rights than an outside consultant. Treat credentials as gold—vault them, rotate them, and audit logins weekly.
2. Encrypt All Sensitive Data in Transit and at Rest
Your applicant information, business plan drafts, financial projections—these are crown jewels. Encrypt them. In flight, use TLS 1.2+ for every API and web interface. At rest, apply AES-256-GCM or equivalent. When you integrate with Torly.ai, our backend ensures compliance across AWS or Azure by default. This is a core item in your application checklist AI, and it reduces risk if any storage bucket or database is ever misconfigured.
3. Validate and Sanitize All Inputs
Generative AI models can be tricked by malicious prompts or payloads. Without proper input validation, your system is exposed to injection attacks or data leakage. In your application checklist AI, ensure:
- Whitelists for accepted document types (PDF, DOCX, etc.)
- Prompt sanitisation to strip out harmful code
- Rate limits on API calls
This step stops rogue scripts and errant characters from slipping into your submission pipeline.
4. Monitor Traffic and API Calls in Real Time
Security is not set and forget. Step four of your application checklist AI demands proactive monitoring. Log every API request to Torly.ai, your cloud provider and any third-party integrations. Flag anomalies like:
- Sudden spikes in request volume
- Unusual IP addresses or geolocations
- Repeated authentication failures
Use alerting tools to notify you immediately. If you see something odd, stop it fast. Secure your Innovator Visa with this application checklist AI
5. Keep All Dependencies Patched and Updated
Outdated libraries are a hacker’s playground. Whether you’re running a Node.js server, Python microservices or Java clients, you must:
- Subscribe to vulnerability advisories (e.g., CVE alerts)
- Automate patch deployment in staging
- Validate updates against your AI model output
This routine maintenance is a critical pillar in your application checklist AI. It ensures that new exploits don’t slip through old versions of your stack.
6. Implement Principle of Least Privilege Everywhere
Your second-factor systems, databases, file storage and CI/CD pipelines all need strict access controls. Apply these best practices:
- Role-based access for developers, legal advisers and founders
- Temporary access tokens for one-off tasks
- Automated revocation for inactive sessions
This principle minimises the blast radius if credentials are compromised and is central to a robust application checklist AI.
7. Perform Regular Security Audits and Penetration Tests
Finally, you can’t secure what you don’t test. Schedule quarterly audits by an external firm or use reputable platforms for penetration testing. Cover:
- Web application layer
- AI model endpoint security
- Infrastructure as code templates
Incorporate findings into your next sprint. This continuous improvement completes your application checklist AI, giving you confidence before submission.
Conclusion: Locking Down Your Visa Victory
The UK Innovator Founder Visa isn’t just about a great idea. It’s about demonstrating bullet-proof processes. Our 7-step security checklist safeguards your data, code and compliance. It’s the playbook we built right into Torly.ai, powered by 24/7 AI support, real-time alerts and dynamic scoring based on evolving Home Office expectations.
Ready to wrap up loose ends? Get your application checklist AI for UK Innovator Visa security
With these measures in place, you’ll submit confidently, knowing every vulnerability has been addressed. That peace of mind? Priceless.