Privacy Compliance Frameworks and Best Practices · May 7, 2026
Building a Robust Data Security Compliance Framework for Innovator Founder Visa Applications
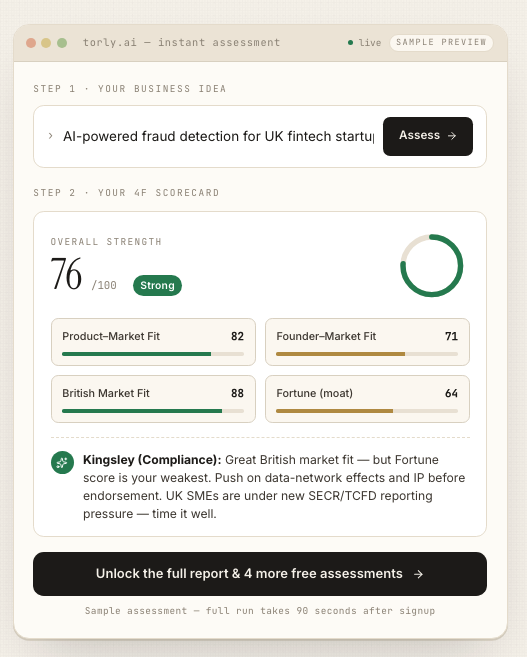
Explore best practices for establishing a strong data security compliance framework and learn how Torly.ai mitigates risks in your visa application process.
Compliance Begins with Confidence: Your Quick Guide to Data Security and Visa Success
Navigating the Innovator Founder Visa process demands more than a stellar pitch—it calls for bullet-proof data security compliance. Without rigorous risk mitigation strategies, you risk delays, rejections or even reputational setbacks. In this article, we unpack the core components of a robust compliance framework, share practical best practices and show how Torly.ai’s AI-powered tools streamline your path to UK endorsement. Ready to see your business idea meet Home Office standards and win trust with endorsing bodies? Risk mitigation strategies with our AI-Powered UK Innovator Visa Application Assistant will take you there.
By the end, you’ll have a clear roadmap: from initial risk assessments through ongoing monitoring, incident response readiness and AI-driven improvement plans. We’ll highlight real examples, simple analogies and bullet lists to keep things punchy. Whether you’re a seasoned founder or fresh off the launch pad, these insights will help you strengthen your documentation, satisfy compliance regs and boost your Innovator Founder Visa approval chances.
Why Data Security Compliance Matters for Innovator Founder Visas
The Home Office’s Expectations
The UK Home Office and endorsing bodies require proof that your venture can protect sensitive data—customer information, proprietary research, investor records. They look for:
- A written data security policy aligned with GDPR, ISO 27001 or similar standards
- Documented risk assessment results
- Encryption for data in transit and at rest
- Role-based access controls
- Established incident response plans
Fail any of these checks and you might see a “needs further information” or worse, a refusal. So, data security compliance isn’t just nice to have—it’s non-negotiable.
Building Trust and Credibility
Imagine you pitch a game-changing AI tool. Then your own data leaks. Ouch. Even minor breaches erode stakeholder confidence. By integrating strong controls up front, you:
- Demonstrate seriousness to endorsing bodies
- Protect your team, customers and IP
- Reduce financial losses and legal exposure
- Foster a culture of accountability
It’s more than ticking boxes. It’s a strategic advantage. And a clear signal: you’re a founder who takes compliance as seriously as innovation.
Core Components of a Robust Compliance Framework
Creating a compliance framework can feel daunting. Let’s break it into four manageable building blocks.
1. Regular Risk Assessments
Think of risk assessments as health checks for your data environment. You:
- Identify assets – Where is sensitive data stored?
- Rank vulnerabilities – What could go wrong? (e.g., weak passwords, outdated systems)
- Evaluate impacts – Financial, reputational, legal
- Prioritise actions – Which issues demand immediate fixes?
Document your findings in a concise report. Re-run assessments at least annually, or whenever major changes occur.
2. Encryption and Data Protection
Encryption scrambles data into an unreadable format without the right keys. Key steps:
- In transit: Use TLS/SSL for web traffic
- At rest: Apply AES-256 for database and file encryption
- Key management: Store encryption keys in a secure vault
Encryption minimises exposure even if intruders breach your defences.
3. Access Controls and User Management
Not everyone needs admin rights. A solid access-control model includes:
- Role-based access: Assign permissions based on job function
- Multi-factor authentication: Add a second verification step
- Periodic reviews: Confirm only authorised users retain access
Effective user management reduces the “insider threat” risk.
4. Incident Response Protocols
When a breach happens, speed is everything. Your incident response plan should detail:
- Clear roles and responsibilities
- Communication channels (internal and external)
- Containment strategies
- Root cause analysis process
- Post-incident reporting and lessons learned
Drill your team periodically. A well-rehearsed response curbs damage and aids regulatory reporting.
After setting up these pillars, consider automating compliance tracking with AI tools. For instance, Torly.ai’s risk-analysis agents continually scan for policy gaps and suggest concrete fixes—so you stay one step ahead.
Integrating AI-Driven Risk Mitigation Strategies
Artificial intelligence isn’t a buzzword here. It’s a force multiplier.
- Continuous monitoring: AI agents detect configuration drifts in real time.
- Predictive analysis: Machine learning spots emerging threats before they materialise.
- Gap identification: Automated reports highlight missing policies or outdated controls.
- Actionable roadmaps: Step-by-step guidance tailored to Innovator Founder Visa requirements.
With Torly.ai’s multi-agent architecture, you combine business evaluation with compliance checks. One agent assesses your venture’s viability, another audits privacy controls, a third maps out board-room ready documentation.
Build Your Endorsement Application with 6 AI Agents
At approximately this halfway mark, it’s vital to reinforce your compliance posture with dynamic, AI-backed insights. Think of Torly.ai as your virtual solicitor for data security—a 24/7 partner ensuring your framework remains airtight. Use risk mitigation strategies in our AI-Powered UK Innovator Visa Application Assistant
Best Practices for Ongoing Compliance Maintenance
A one-off setup won’t cut it. You need continuous care.
Continuous Monitoring and Audits
- Schedule automated scans
- Track metrics (incident frequency, patch latency)
- Conduct internal audits quarterly
Training and Awareness Programmes
- Run interactive staff workshops
- Issue regular security bulletins
- Simulate phishing exercises
Policy Review and Updates
- Update policies for new regulations
- Archive obsolete procedures
- Engage external consultants for fresh perspectives
By institutionalising these practices, you embed security into your company’s DNA.
Overcoming Common Challenges in Compliance
Even the best frameworks face hurdles.
Resource Constraints
Startups often juggle budgets and manpower. Mitigate this by:
- Leveraging AI tools to automate routine tasks
- Outsourcing specialised audits on demand
Complexity of Regulations
UK, EU and sector-specific regs can overlap. A centralised policy library helps you:
- Map obligations to controls
- Spot inconsistencies
- Streamline compliance efforts
Evolving Threat Landscape
Cyber threats morph daily. Counteract this by:
- Subscribing to threat-intelligence feeds
- Participating in founder communities
- Updating defences promptly
With the right mix of automation, expert guidance and proactive planning, these challenges become manageable.
Conclusion: Your Path to Endorsement-Ready Confidence
Crafting a robust data security compliance framework is a journey, not a checkbox. From risk assessments through encryption, access controls and incident response, each step builds your credibility with the Home Office and endorsing bodies. By weaving in AI-driven agents, you gain real-time insights, predictive threat analysis and custom action plans—maximising your Innovator Founder Visa approval prospects.
Remember, compliance underpins trust. It shields your idea, your investors and your customers. Start with the fundamentals, layer on AI automation and keep your policies alive with regular reviews. Your innovative venture deserves nothing less than an airtight security posture.
Apply risk mitigation strategies with Torly.ai’s AI-Powered UK Innovator Visa Application Assistant