Compliance Tools and Platforms · April 15, 2026
Visa Data Security: Implementing HITRUST Cybersecurity Standards in AI Tools
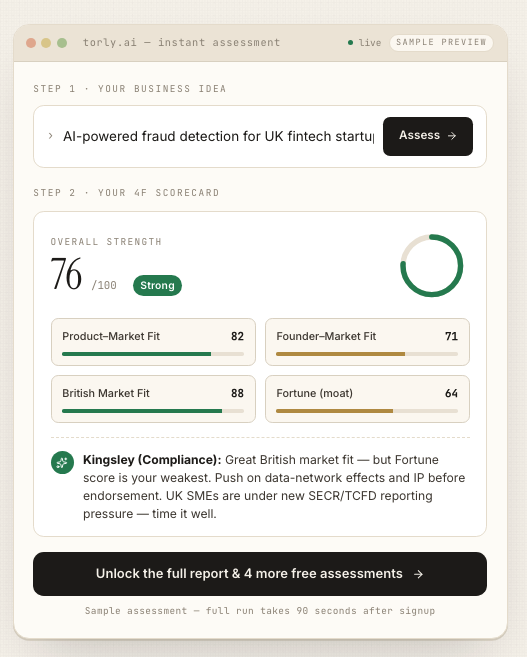
Protect your Innovator Visa application data with Torly.ai’s AI risk management features aligned to HITRUST cybersecurity standards for maximum security.

Securing Visa Application Data with HITRUST Cybersecurity
Securing personal and business data in visa applications is no small task. You need a shield strong enough to fend off threats and flexible enough to adapt to new risks. That is where HITRUST cybersecurity steps in. By weaving HITRUST’s risk-based controls into your AI tools, you create a fortress around sensitive information. It makes sure that every byte of data you process meets rigorous standards and stays protected.
Looking for a seamless way to safeguard your Innovator Visa application with HITRUST cybersecurity? AI-Powered UK Innovator Visa Application Assistant with HITRUST cybersecurity delivers just that. It wraps your data in proven controls while guiding you through every step, from eligibility checks to final submission. No more guesswork, no more sleepless nights.
Why AI Tools Need Robust Data Protection
AI-driven visa platforms handle names, financials, business plans and legal documents. A slip in security can expose:
- Personal identity details
- Proprietary business ideas
- Financial records
- Sensitive legal filings
Cyber attackers constantly evolve. They probe for weak spots in software and cloud environments. Without strong safeguards, your AI assistant could be the next target. Adopting HITRUST cybersecurity helps you lock down those gaps. It brings industry best practices and aligns everything to a single, coherent standard.
Overview of HITRUST Cybersecurity Standards
At its core, HITRUST is about consistency and efficiency. The HITRUST CSF Framework is a threat-adaptive control library. It harmonises more than 60 global regulations, standards and frameworks. You don’t juggle ISO, NIST and GDPR separately. They’re all mapped into one set of requirements. That makes risk-based assessments faster and more reliable.
Building your AI solution around HITRUST means you:
- Apply proven controls in data encryption and access
- Perform regular risk assessments with clear metrics
- Sustain compliance across evolving threats
That’s peace of mind for you and everyone whose data you handle.
The HITRUST CSF Framework
The HITRUST CSF creates a unified approach. Key aspects include:
- A catalogue of 19 control categories
- Over 300 individual control requirements
- Mapping to 60+ standards (NIST, ISO, HIPAA, GDPR)
- Scalable risk tiers for different organisation sizes
This makes it ideal for platforms like Torly.ai. You gain a tailored set of controls that match your specific risk profile.
Core Principles and Controls
Controls in HITRUST cybersecurity revolve around:
- Information protection policies
- Access management and authentication
- Encryption of data in transit and at rest
- Incident response and recovery planning
- Continuous monitoring and auditing
Each control ties back to real legal or regulatory references. You’ll know exactly why it’s there and how to test it.
Aligning Torly.ai’s AI Risk Management with HITRUST
Torly.ai offers a multi-layered approach to visa readiness. It uses advanced AI reasoning to evaluate:
- Business Idea Qualification
- Applicant Background Assessment
- Gap Identification and Action Roadmap
By embedding HITRUST cybersecurity into these assessments, Torly.ai not only helps you shape a winning Innovator Founder Visa application. It also secures every data point you feed into the system.
Business Idea Qualification and Data Security
First, Torly.ai tests if your business idea is innovative, viable and scalable. While analysing your concept, the platform:
- Encrypts documents end-to-end
- Applies access controls by role
- Logs every action for a tamper-proof audit trail
That audit trail aligns with HITRUST cybersecurity controls around accountability and logging.
Applicant Background Assessment Under HITRUST Guidelines
Next, your background gets reviewed. Torly.ai’s AI agents check expertise, track record and EB endorsement likelihood. Meanwhile, your personal and professional data remains under strict guard. The system uses:
- Multi-factor authentication
- Automated risk scoring for suspicious activity
- Periodic credential rotation
All of which map directly to HITRUST’s access and identity management requirements.
Gap Identification & Remediation with AI
Finally, Torly.ai highlights gaps in your application. It suggests improvements for your model, market pitch and documentation. Plus, it recommends specific security enhancements:
- Data classification schemes
- Endpoint protection setups
- Vendor risk reviews
Ready to streamline both your business plan and your security posture? Build your Business Plan NOW with our Desktop APP
Implementation Steps for HITRUST Compliance in AI Visa Platforms
Rolling out HITRUST cybersecurity in an AI solution may sound daunting. Here’s a clear path:
- Perform a scoping exercise
– Identify data flows and storage points
– Classify information by sensitivity - Conduct an initial risk assessment
– Use HITRUST’s tiered risk model
– Score each control requirement - Map existing controls
– Note gaps between current setup and HITRUST CSF
– Prioritise high-risk areas - Develop policies and procedures
– Document data handling guidelines
– Train your AI agents to log key events - Implement technical controls
– Encryption, authentication, endpoint protection
– Automated monitoring and alerting - Validate compliance
– Run self-assessments or engage a HITRUST assessor
– Address any residual risks - Maintain continuous improvement
– Update controls as threats emerge
– Leverage AI to refine risk scoring
This step-by-step guide is exactly what Torly.ai’s experts follow under the hood. You get a ready-made framework without reinventing the wheel.
Benefits of Combining HITRUST Standards with AI Visa Solutions
Adopting HITRUST cybersecurity in your AI-driven visa platform unlocks clear advantages:
- Consistent compliance across multiple regulations
- Faster onboarding for applicants
- Stronger trust signals for endorsing bodies
- Automated risk management with AI insights
- Improved incident response times
When your data security ticks all these boxes, you can focus on building your business and getting your Innovator Visa approved.
Real-World Success Stories
Several forward-thinking entrepreneurs have already benefited:
- A fintech founder cut application review time by 50%
- A healthcare startup avoided a data breach during endorsement prep
- An edtech team maintained full compliance as regulations changed
All of them used Torly.ai. They tapped into AI-driven checks, gap analysis and robust data controls. And they never had to worry about loose ends in their security framework.
Ready to level up both your business plan and your data protection? Try the TorlyAI BP Builder APP for tailored visa business planning
Testimonials
“Torly.ai’s built-in security checks gave me peace of mind. I knew my data was guarded by top-tier HITRUST cybersecurity controls while I focused on refining my business plan.”
— Emma Turner, Fintech Entrepreneur
“I appreciated the clear guidance on compliance. The AI would flag any gaps in my documents and suggest fixes. Plus, the platform’s audit logs are rock solid.”
— Raj Patel, HealthTech Founder
Conclusion
Implementing HITRUST cybersecurity standards in your AI visa platform is not optional. It’s essential for protecting sensitive applicant data and maintaining regulatory compliance. By adopting a unified framework like the HITRUST CSF, you simplify risk management, align with global regulations and build trust with endorsing bodies.
If you’re ready to secure your Innovator Visa journey with advanced AI and robust security, it’s time to take action. Get started with our AI-Powered UK Innovator Visa Application Assistant and HITRUST cybersecurity